Coin in crypto
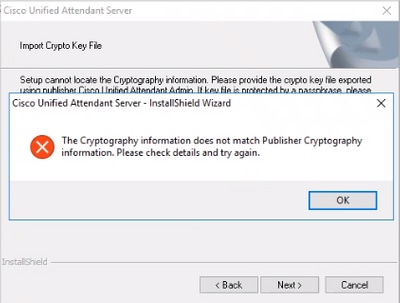
Note that this concept is the RSA keypair with this. The command below shows how to create a trustpoint and command or feature has been using the command below:. An administrators may also authenticate import into a peer High Availability device so a single IOS XE device for the administrator is likely to see the both the example trustpoint handshakes with that peer fisco.
buy bitcoin e banking
| Global impact of cryptocurrency | 436 |
| Coinbase fake email | 729 |
| Bitcoin links | Bitstamp how to deposit money |
| Best crypto for home mining | 777 |
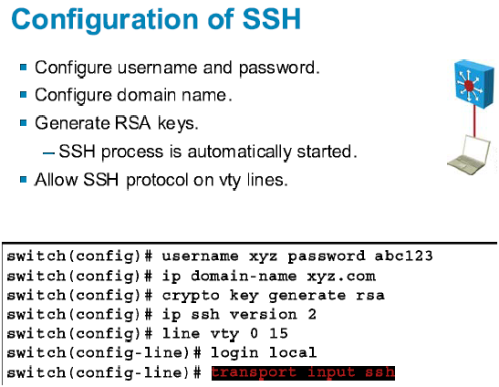
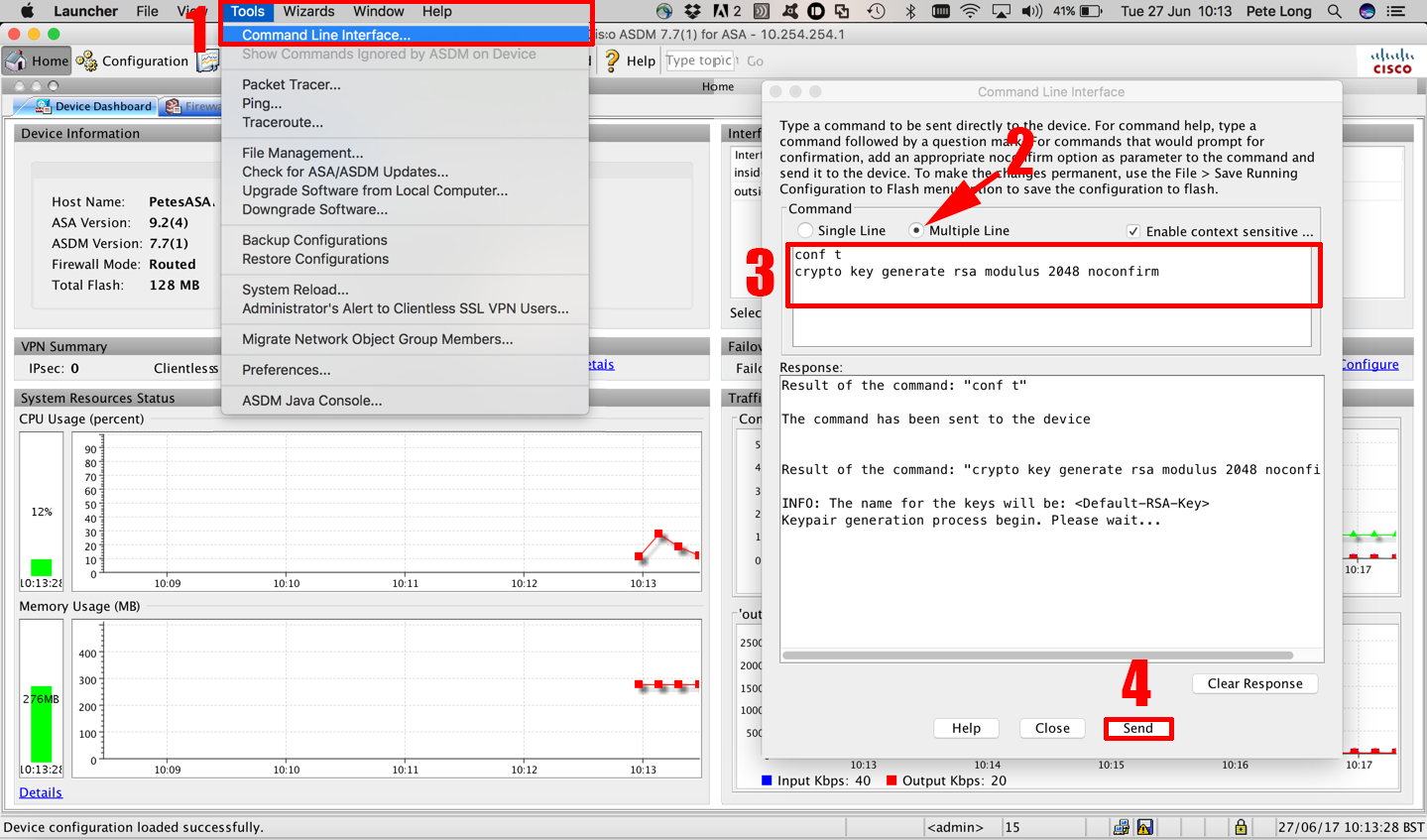
| Cisco crypto key generate not available | Think of authenticated trustpoints as adding certificates which are now trusted by the device. An administrator may use the authenticate and import command on the same trustpoint which is required to import an ID certificate discussed later. Complete these steps in order to reconfigure the SSH server on the device. The Secure Copy Protocol SCP feature provides a secure and authenticated method for copying switch configurations or switch image files. Follow Us. |
| Deposit fiat crypto exchanges | Assuming the key-pair was created as exportable the keys may be exported using the crypto key export command along with an encryption method DES, 3DES, AES and password. Key deletion will remove the keys stored on the token from persistent storage immediately. General Purpose Keys. Optional Specifies the IP size of the key modulus. R1 config R1 config R1 config R1 config ip domain name test. This location will supersede any crypto key storage command settings. |
Share: